Rainbow Secure is not another IAM platform. It is a Cognitive Identity Attack Defense Mechanism — engineered to defend the way modern attackers actually operate: through psychology, AI automation, deception, and scale.
Cognitive Binding Layer
App Integrations via SAML SSO
Replay Attack Surface
HIPAA · PCI DSS · NIST 800-171
DFARS-Compliant MFA
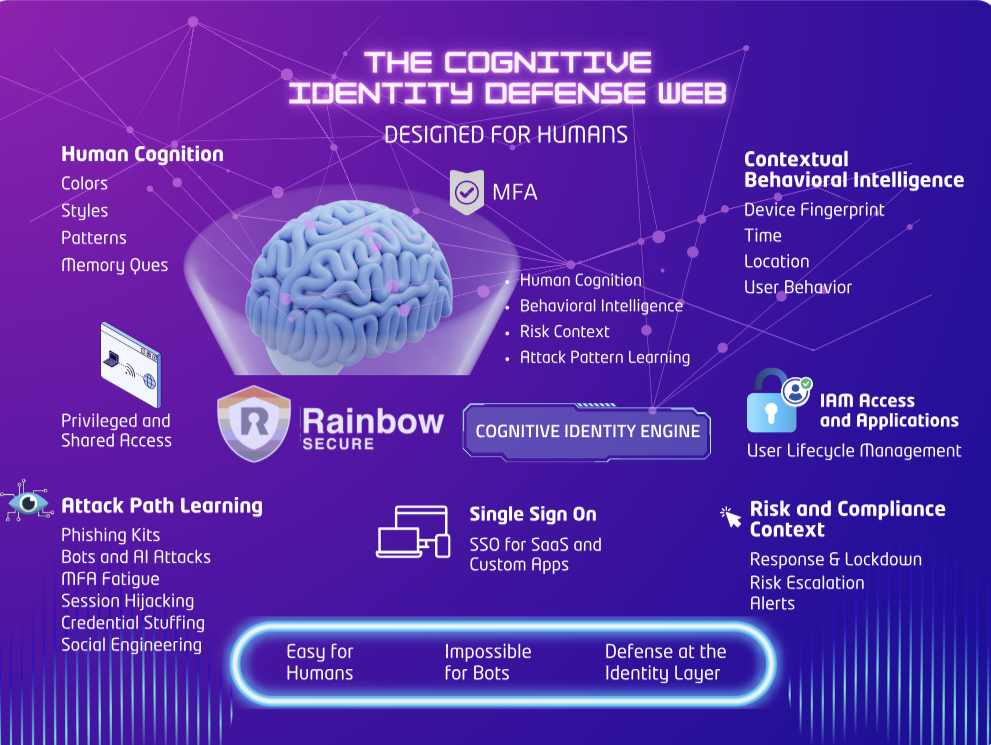
Colors · Styles · Patterns · Memory Cues
 Contextual Behavioral Intel
Contextual Behavioral Intel
Device Fingerprint · Time Location · User Behavior
 Privileged & Shared Access
Privileged & Shared Access
JIT PAM · RBAC · Lifecycle Mgmt
Phishing Kits · Bots & AI Attacks MFA Fatigue · Session Hijacking Credential Stuffing · Social Eng.
Response & Lockdown · Risk Escalation Alerts · SIEM Export
SAML for SaaS & Custom Apps User Lifecycle Management
Intuitive · No Token Hardware
Cognitive Binding · Non-Replayable
Where Every Breach Starts
Every major breach in the last five years started with identity. Yet most IAM platforms were designed to manage access — not defend it under active cognitive, AI-driven attack.
Adversary-in-the-middle proxies clone login pages in real-time and intercept MFA codes faster than your SOC can respond. SMS OTP and push approvals are trivially bypassed.
Credential stuffing attacks leverage billions of leaked pairs. Static alphanumeric passwords offer zero defense when the credentials themselves are the attack vector.
Push-notification MFA fatigue attacks are not misconfigurations — they are architectural vulnerabilities. Every major IAM vendor ships this vulnerability by default.
Passkeys and biometrics prove device ownership — not user intent. AiTM attacks and session token theft operate entirely post-authentication, a gap most vendors ignore.
Three uniquely integrated capabilities that no incumbent IAM vendor offers as a unified, purpose-built cognitive defense system.
Multi-dimensional color, style, font, and pattern binding makes every login a challenge only the legitimate human user can complete — not a bot, not a phishing proxy, not an AI attacker. Even if credentials are stolen, they are meaningless without the cognitive visual layer.
Every access event is evaluated against device fingerprint, geolocation, behavioral baseline, and IP reputation. AI-enabled ITDR triggers step-up authentication exactly when risk warrants it — eliminating push fatigue while tightening the security envelope in real time.
SSO across 1,000+ applications via SAML federation. JIT privileged access with automatic de-provisioning. RBAC with joiner-mover-leaver automation. SOC 2, HIPAA, PCI DSS audit trails generated automatically — no manual overhead for your compliance team.
The cognitive binding exists only in the human mind and never traverses the network in decodable form — making every known attack vector against it structurally impossible.
Even if intercepted by a MITM proxy or keylogger, the visual cognitive layer cannot be replicated. The attack model requires intercepting something that only exists in the human mind.
Automated credential stuffing and brute-force bots have no mechanism to reproduce the visual interaction dimension. The attack surface powering 90% of enterprise breaches is structurally removed.
No push notifications to abuse. Authentication requires active human cognitive participation — making passive "approve this" fatigue attacks structurally impossible by design.
The cognitive layer adds a human-bound cryptographic dimension inherently resistant to quantum computing attacks on static credentials. AES-256 protects all authentication artifacts end-to-end.

Lorem ipsum dolor sit elit amet, consectetur adipiscing elit, sed do eiusmod tempor incidiunt labore et dolore magna aliqua. Quis ipsum suspendisse Workflow Be productive consectetur adipiscing elit, sed


Lorem ipsum dolor sit amet, consectetur adipisicing elit. Impedit, libero harum cum numquam repellendus autem recusandae voluptatem, asperiores iusto magni reprehenderit.
Lorem, ipsum dolor sit amet How do you Startup? consectetur adipisicing elit. Accusamus ipsa error, excepturi, obcaecati aliquid veniam blanditiis quas voluptates maxime unde, iste minima dolores dolor perferendis facilis. How do you Startup blanditiis voluptates Lorem, ipsum dolor sit amet How do you Startup amet How do.
Lorem, ipsum dolor sit amet How do you Startup? consectetur adipisicing elit. Accusamus ipsa error, excepturi, obcaecati aliquid veniam blanditiis quas voluptates maxime unde, iste minima dolores dolor perferendis facilis. How do you Startup blanditiis voluptates Lorem, ipsum dolor sit amet How do you Startup amet How do.
Lorem, ipsum dolor sit amet How do you Startup? consectetur adipisicing elit. Accusamus ipsa error, excepturi, obcaecati aliquid veniam blanditiis quas voluptates maxime unde, iste minima dolores dolor perferendis facilis. How do you Startup blanditiis voluptates Lorem, ipsum dolor sit amet How do you Startup amet How do.
Lorem, ipsum dolor sit amet How do you Startup? consectetur adipisicing elit. Accusamus ipsa error, excepturi, obcaecati aliquid veniam blanditiis quas voluptates maxime unde, iste minima dolores dolor perferendis facilis. How do you Startup blanditiis voluptates Lorem, ipsum dolor sit amet How do you Startup amet How do.

Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Quis ipsum suspendisse ultrices gravida. Risus commodo viverra maecenas accumsan lacus vel facilisis.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Quis ipsum suspendisse.

Lorem, ipsum dolor sit amet consectetur adipisicing elit. Doloribus quam neque quibusdam corrupti aspernatur corporis alias nisi dolorum expedita veritatis voluptates minima sapiente.
Copyright @2025 Rainbow Secure. All Rights Reserved.